Tor
Welcome to the exciting world of Tor! This page will get you up and running, in the fewest steps possible. For now, all you need to know is that Tor is a great tool for anonymity and privacy online.
Get Tor Installed
The first step is to download Tor Browser. The Tor Project offers quite a few packages for download, start with picking the “Tor Browser package” for your operating system.
At the time of this being written, the Tor Browser only supports Windows, macOS, Linux, and Android. For iOS users, “Onion Browser” is a free and open source alternative to Tor Browser encouraged for use by the Tor Project.
Once you have downloaded the Tor Browser, proceed to follow the instructions below, depending on your operating system.
Windows Instructions
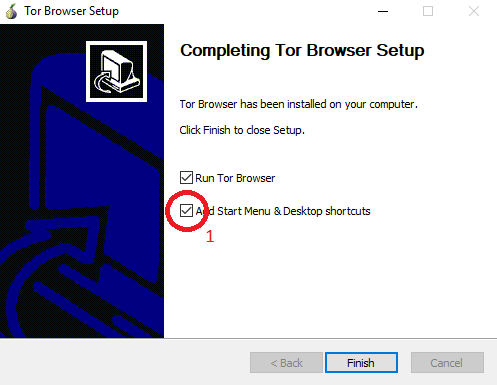
After you’ve downloaded the Tor Browser installer, double click on the installer to start the installation process. Choose your language and select where you want to save the bundle to then click “OK”. At least 181 MB free space must be available in the location you select. If you want to leave the bundle on the computer, saving it to the Desktop is a good choice. If you want to move it to a different computer or limit the traces you leave behind, save it to a USB disk. Once finished, make sure that you check the box labeled “Add Start Menu & Desktop shortcuts” (1) for an easy way to start the browser.
See the Using Tor section below for how to use Tor.
macOS
After you’ve downloaded the Tor Browser Bundle, simply click on it to begin the installation. macOS will automatically unarchive it and you will have a TorBrowser application in your chosen language (for example, TorBrowser_en-US.app). Click the TorBrowser application to launch the connection wizard. Once connected to Tor, it will launch Tor Browser.
![]()
See the Using Tor section below about how to use Tor.
Linux
Download the architecture-appropriate file, save it somewhere such as “~/Downloads”. To extract the files you may use graphical tools like archive manager, Ark or Xarchiver. Alternatively you can extract on the command line:
- For 32-bit Linux:
tar -xvf ~/Downloads/tor-browser-linux32-X.X.X_LANG.tar.xz - For 64-bit Linux:
tar -xvf ~/Downloads/tor-browser-linux64-X.X.X_LANG.tar.xz
X.X.X being the version of the browser archive and LANG being the language you are using. For example, if you are installing Tor Browser version 9.0.5 for the english language on a 64-bit machine, you would use “tor-browser-linux64-9.0.5_en-US.tar.xz” as the file name.
Once extracted, navigate inside the new folder created by the extraction (“tor-browser_en-US”) and use the command chmod to turn the file `start-tor-browser.desktop` into an executable:
cd tor-browser_en-US
chmod +x start-tor-browser.desktopYou can now execute the file with the command ./start-tor-browser.desktop, or by double clicking the file in a file manager, to launch the connection wizard.

Linux users may prefer “torbrowser-launcher”. This tool ensures your Tor Browser is legitimate and up to date in an easy manner.
Don’t extract Tor Browser as root.
Android
Tor Browser is avaliable for download from the “Google Play store” and as an APK file. Install the application from the Play Store or download or manually install the APK file if you do not wish to use the Play Store.
Using Tor
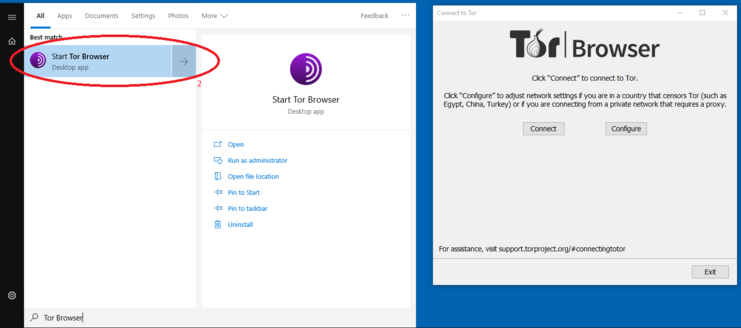
Once extraction or installation is complete, you can type “Tor Browser” from your Windows start menu then click on the Start Tor Browser (2) application (it may be called “Start Tor Browser.exe” on some systems) or click on the newly created desktop icon. On macOS, just start Tor Browser from the Applications menu.
If you are using Linux, you will need to navigate to the extracted Tor Browser directory and double click “start-tor-browser” (this sometimes can end in “.desktop”). From a terminal, you can also navigate to the Tor Browser directory and run ./start-tor-browser.desktop --register-app in order to add Tor Browser to your Applications menu.
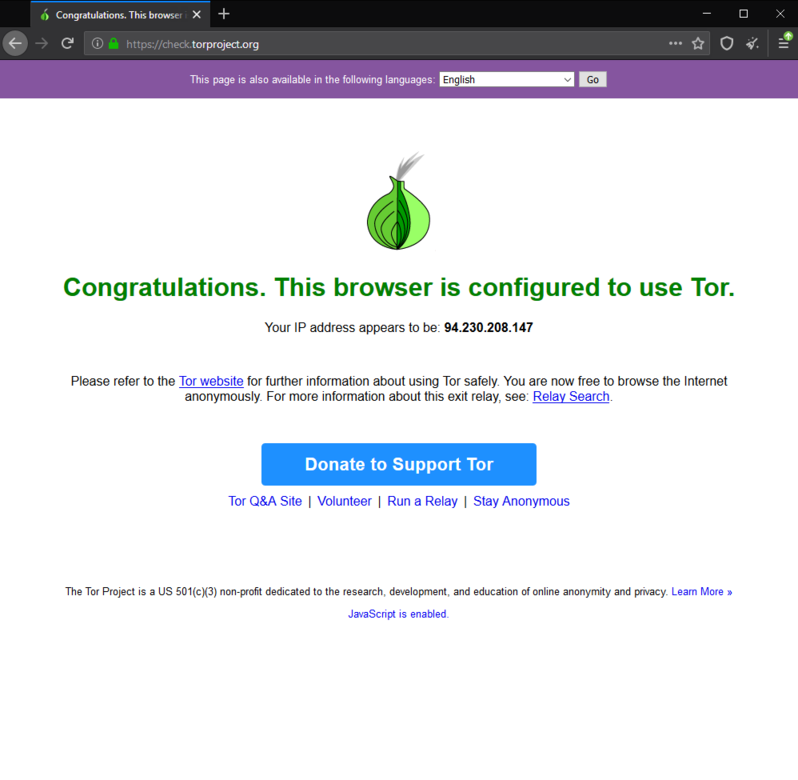
Once Tor is ready, Tor Browser will open a menu with buttons “Connect” and “Configure”. Unless you live in an oppressive state that censors internet or if you would like to use a proxy to connect to the Tor network, this can be ignored. Once “Connect” is clicked, Tor will establish a connection and will automatically open a Firefox like web browser. Only web pages visited through Tor Browser will be sent via Tor. Other web browsers such as Google Chrome and Firefox are not affected by Tor. Before browsing, it is a good idea to ensure you are connected to the Tor network. To reduce the risk of confusion, don’t run the normal Firefox web browser while using the Tor Browser, as its better to close existing Firefox windows before starting.
Once you are finished browsing, you can close out of the browser like you normally would. For privacy reasons, the list of web pages you visited and any cookies will be deleted.
Riseup’s Tor Onion Services
Tor makes it possible for not just users to hide their locations, but servers as well. You can access Riseup’s services via our Tor Onion Service addresses. Whenever you see a URL that ends with .onion, that’s a Tor onion service. If you are running Tor, you can simply put that onion address where you would normally put the regular address (for example, as a URL in your Tor enabled web browser) and it will use the Tor network to get to our servers.
The following is a list of Riseup’s Tor onion services. If you have trouble verifying this, try downloading and verifying this file:
-----BEGIN PGP SIGNED MESSAGE----- Hash: SHA512 Riseup only supports v3 hidden/onion services. These are faster, and more secure, and have a longer .onion address. The v2 onion services that we used to list here are still operational, but we will not be publishing them here, as we do not want people to use them. The v2 onion services will no longer be operational after April, 2021. If you use the v2 addresses, please transition to the longer v3 addresses as soon as you can. riseup.net: vww6ybal4bd7szmgncyruucpgfkqahzddi37ktceo3ah7ngmcopnpyyd.onion (port 80) help.riseup.net: vww6ybal4bd7szmgncyruucpgfkqahzddi37ktceo3ah7ngmcopnpyyd.onion (port 80) lists.riseup.net: 7sbw6jufrirhyltzkslhcmkik4z7yrsmbpnptyritvz5nhbk35hncsqd.onion (port 80) mail.riseup.net: 5gdvpfoh6kb2iqbizb37lzk2ddzrwa47m6rpdueg2m656fovmbhoptqd.onion (ports 25, 80, 110, 143, 465, 587, 993, 995) imap.riseup.net: 5gdvpfoh6kb2iqbizb37lzk2ddzrwa47m6rpdueg2m656fovmbhoptqd.onion (ports 143, 993) pop.riseup.net: 5gdvpfoh6kb2iqbizb37lzk2ddzrwa47m6rpdueg2m656fovmbhoptqd.onion (ports 110, 995) smtp.riseup.net: 5gdvpfoh6kb2iqbizb37lzk2ddzrwa47m6rpdueg2m656fovmbhoptqd.onion (ports 25, 465, 587) mx1.riseup.net: aj3nsqqcksrrc5cye5etjsoewz6jrygpekzwoko3q6wyxjlb3dgasfid.onion (port 25) pad.riseup.net: kfahv6wfkbezjyg4r6mlhpmieydbebr5vkok5r34ya464gqz6c44bnyd.onion (port 80) share.riseup.net: 2pyimbpxocupne6nbekma4dygkobl36sblei6ttknbm4kfh3r7jlpzyd.onion (port 80) account.riseup.net: 3xeiol2bnhrsqhcsaifwtnlqkylrerdspzua7bcjrh26qlrrrctfobid.onion (port 80) we.riseup.net: zkdppoahhqu5ihjqd4qqvyfd2bm4wejrhjosim67t6yopl77jitg2nad.onion (port 443) 0xacab.org wmj5kiic7b6kjplpbvwadnht2nh2qnkbnqtcv3dyvpqtz7ssbssftxid.onion (port 80) -----BEGIN PGP SIGNATURE----- iQJKBAEBCgA0FiEETgeRJo98Z+q+iPGwMEPitxOado4FAmMPg0EWHGNvbGxlY3Rp dmVAcmlzZXVwLm5ldAAKCRAwQ+K3E5p2jrauD/9mwJmEzJtyhYSjZFYt+kI/u4Za ghKgX+IvNpbKGTCzSiL/aiUjDi5ayOPy0ICU1cYEggPC88+ccEUZRPgOl88A6ija vOjijtF3RN7OXCTpSgmZXDqf+vt6K+y2bkg0SpHWTzVVGwNg2nckAd2Kt0Wh/Fz0 pixeuF3Pbfq2s0wrlEPARYMYR96rTCSglTIiuieUoH/NO+ECGpsqDJk/0/QBbhNv 4/5aNfBNGzjDudW8XoLWVS/nj73zw/zH31CbzE7Bh5QGIh2WcvY7MtJmWPDIA1tm fax/2oGdR+NCoNTt4rtMt/TN4SNtX70FlBMfh0L86dzYjYe42pcBi0k/GON24mn1 xmqqqrwSZk0oiQ/qXAxA5LozFqk/PO9UcYjfUqJbYgvOpEMFJIC7h6d/FCRLEct1 ileg7MraCSBfVpBpSO3SkrPW2ELLqtViY1bNCCRgGapcHm/M9wBulp6eR6ksIBxS Z+h4y4+moPaH9HthbnD4VXcGNqHXDJda8929rKTM4m8R+k6wWBtYIjwDy3bD0Rwc zJOiIfI+mdCK16ZJG+r75W9Q3IStlp3bcFUASqdIDWAWa7Ul+EWlyVK1JRoB088R iuIawzcLwHEZSdfSkEGnie/vfHRDVB3GkaKhOYb/sYwyU9qgGlPX5HVu6D3rWm8b CcOWwrVGsmY4Tpy1OA== =xZQR -----END PGP SIGNATURE-----
Warnings and Notes
First, be aware: Tor can be very slow, sometimes you wont notice that it is slow, but other times you will think that things aren’t working at all. The experience varies as Tor changes how your connection is routed. This is because your connection is being routed through at LEAST three computers. If two of those computers are blazing fast, but the third is a snail, your data will only move as fast as the snail can handle.
Second, while Tor itself may be quite secure, other software on your computer may not be. You need to change some of your habits, and reconfigure your software! Tor by itself is NOT all you need to maintain your anonymity. Further information is available at the Tor Project website, in their documentation section. Please read this information carefully before doing anything potentially unsafe on the Tor system.
Third, you don’t need SSL/TLS in an onion address (ie. https) since it’s a complete encrypted tunnel with perfect forward secrecy. Because it doesn’t hurt having extra protections, you can still connect using the SSL/TLS protected channels, just be aware that the certificate will not validate (because the hostname will be *.onion) and you would need to perform the validation manually.
Some text in this document is transposed from the Tor Project’s website via Creative Commons Attribution 3.0.
Additional Resources
- The Surveillance Self Defense project over at the Electronic Frontier Foundation is a plethora of helpful and interesting information. Especially relevant is their Tor page.
- The Tor Project’s website will be able to answer almost all of your questions concerning the Tor project, and how to use the software effectively.